Full paper presented at the 40th IEEE Symposium on Security and Privacy on May 20-22, 2019 at San Francisco (CA). Check out the talk preview video!
Abstract
HTTPS aims at securing communication over the Web by providing a cryptographic protection layer that ensures the confidentiality and integrity of communication and enables client/server authentication. However, HTTPS is based on the SSL/TLS protocol suites that have been shown to be vulnerable to various attacks in the years. This has required fixes and mitigations both in the servers and in the browsers, producing a complicated mixture of protocol versions and implementations in the wild, which makes it unclear which attacks are still effective on the modern Web and what is their import on web application security. In this paper, we present the first systematic quantitative evaluation of web application insecurity due to cryptographic vulnerabilities. We specify attack conditions against TLS using attack trees and we crawl the Alexa Top 10k to assess the import of these issues on page integrity, authentication credentials and web tracking. Our results show that the security of a consistent number of websites is severely harmed by cryptographic weaknesses that, in many cases, are due to external or related-domain hosts. This empirically, yet systematically demonstrates how a relatively limited number of exploitable HTTPS vulnerabilities are amplified by the complexity of the web ecosystem.
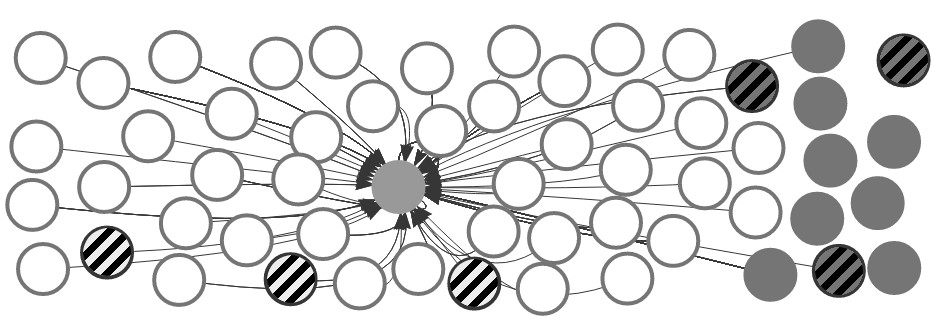
An anonymized top Alexa website (central circle) and its sub-domains (gray, on the right) and dependencies (white, with arrows). The website is entirely deployed over HTTPS, but becomes insecure due to three vulnerable sub-domains and three vulnerable dependencies (striped circles).
Experimental Results
We crawled the first 10,000 websites according to the Alexa top 1M list (retrieved on July 20, 2018) served over HTTPS. Their sub-resources and related domains added up to 90,816 more hosts that underwent a vulnerability analysis, completed at the beginning of August 2018. We discovered TLS vulnerabilities in 5,574 hosts (5.5%):
- 4,818 vulnerable to MITM
- 733 vulnerable to full decryption
- 912 vulnerable to partial decryption
As a consequence of these cryptographic vulnerabilities, we found that:
- 898 websites are fully compromisable, allowing for script injection, while 977 websites present low integrity pages that the attacker can tamper with. Fully compromisable sites include e-commerce sites, e-banking services and other major websites. 660 out of the 898 compromisable websites (73.5%) include external scripts from vulnerable hosts, thus empirically demonstrating that the complexity of web applications enormously amplifies their attack surface;
- 10% of the detected login forms have confidentiality issues, which may enable password theft. 412 websites may be subject to cookie theft, exposing to session hijacking, and 543 websites are subject to cookie integrity attacks. Interestingly, we found that more than 20% of the analyzed domain cookies can be potentially leaked, suggesting that the organization of web applications as related sub-domains amplifies their attack surface and needs to be carefully analyzed;
- 142 websites include content from vulnerable hosts of one popular tracker and thus expose users to profiling attacks. Remarkably, this privacy attack can be amplified by the previous finding on compromisable websites, so as to affect up to 968 websites. This shows once more that attacks against TLS on external resources may expose otherwise secure websites to severe threats.
Media Coverage
- HTTPS Isn’t Always as Secure as it Seems, Lily Hay Newman on Wired.com, 28 March 2019
- False sense of security? HTTPS is no panacea, researchers warn, Catherine Chapman on The Daily Swig, 16 May 2019